Queue management system security refers to the practices and technologies that protect customer data, prevent unauthorized access, and ensure service integrity. Key pillars include multi-factor authentication (MFA), role-based access control (RBAC), and data protection measures like encryption.
Queue management systems handle sensitive customer information every day. A bank branch queue system knows customer names, account types, and service histories. A healthcare queue system stores patient identifiers, appointment details, and medical record references. A government service queue system may collect national ID numbers and benefit eligibility status.
This data is valuable to attackers.
A breach can expose thousands of records, leading to identity theft, regulatory fines, and permanent reputational damage. Insecure systems also risk operational disruption. An attacker who gains access could change queue priorities, delete appointments, or lock staff out of the system.
As organizations deploy queue management across branches, clinics, and contact centers, security becomes a top concern.
Enterprise customers require proof that their vendors protect data. Three pillars form the foundation of Queue Management System Security: multi-factor authentication (MFA), role-based access control (RBAC), and data protection. These controls work together to prevent unauthorized access, limit damage if a breach occurs, and keep customer information safe.
Wavetec builds these security features into its queue management system, offering enterprise-grade protection for organizations in banking, healthcare, and government.
Why Security Is Critical in Queue Management Systems

Queue management systems are not just about tickets and wait times. They are databases of customer interactions. Every check-in creates a record. Every service transaction updates that record.
Over time, the system accumulates a rich dataset of who visited, when, why, and what happened. This data is sensitive for several reasons.
- First, queue systems often integrate with CRM, healthcare information systems, and core banking platforms. Through these integrations, they can access even more detailed customer data. A queue system connected to a bank’s core platform may display account balances and transaction histories to tellers. A queue system linked to a hospital HIMS may show patient diagnoses and medications.
- Second, queue systems are accessed by many users across multiple locations. Branch staff, managers, regional supervisors, and IT administrators all log into the system. Each user has different data needs and different risk profiles. Without proper controls, a teller could view manager dashboards. A branch manager could modify queues at other branches. A compromised low-level account could be used to escalate privileges.
- Third, queue systems are increasingly cloud-based and accessed over the internet. This convenience expands the attack surface. Attackers can target the system from anywhere, not just from inside a branch. Phishing attacks can steal credentials. Vulnerabilities in web interfaces can be exploited. Without strong security, cloud deployment introduces new risks.
- The risks of insecure systems are severe. Data breaches expose customer information, leading to identity theft, fraud, and regulatory penalties under laws like GDPR, HIPAA, and PCI DSS. Unauthorized access can disrupt operations, with attackers changing queue rules, deleting appointments, or locking out staff. Reputational damage can be permanent, as customers lose trust in organizations that cannot protect their data. Enterprise customers may terminate contracts with vendors that suffer breaches.
Security is also a prerequisite for enterprise adoption. Large banks, hospital networks, and government agencies require proof of security controls before deploying a queue system.
They audit vendors for MFA, RBAC, encryption, and compliance certifications. A queue system without these features cannot compete in enterprise markets.
For more on securing customer interactions, see this article on customer interaction management strategies and benefits.
What Is Multi-Factor Authentication (MFA)?
Multi-factor authentication (MFA) is a security method that requires users to provide two or more verification factors to gain access to a system. The goal is to create layered defense. Even if an attacker steals a user’s password, they cannot log in without the additional factor.
MFA typically combines three types of factors.
- Something you know is a password or PIN.
- Something you have is a physical device such as a smartphone, hardware token, or smart card.
- Something you are is a biometric characteristic such as fingerprint, facial recognition, or voice pattern.
Most queue management systems implement MFA using a password plus a one-time code sent via SMS or generated by an authenticator app. Some advanced systems also support biometrics on mobile devices.
- When a user attempts to log in, the system first verifies their password.
- If correct, it sends a challenge for the second factor.
- The user must enter the one-time code from their phone.
- Only after both factors are successfully verified does the system grant access.
This process adds a few seconds to login but blocks 99.9% of automated attacks, credential stuffing, and many phishing attempts.
MFA is especially important in SaaS and queue management systems because these systems are accessed over the internet. Passwords alone are insufficient. Users reuse passwords across sites, write them down, or fall for phishing emails that steal credentials. MFA neutralizes these weaknesses.
For administrators and privileged users, MFA should be mandatory. Branch managers, regional directors, and IT staff have increased permissions. If their accounts are compromised, attackers can cause widespread damage. Some organizations also require MFA for all users, including tellers and receptionists. The incremental security is worth the minor inconvenience.
In queue management systems, MFA can be implemented at the application level, with the login page requiring a second factor. It can also be integrated with single sign-on (SSO) providers such as Okta, Azure AD, or Google Workspace, which already enforce MFA policies. This approach centralizes authentication management and reduces user friction.
Role-Based Access Control (RBAC) in Queue Systems
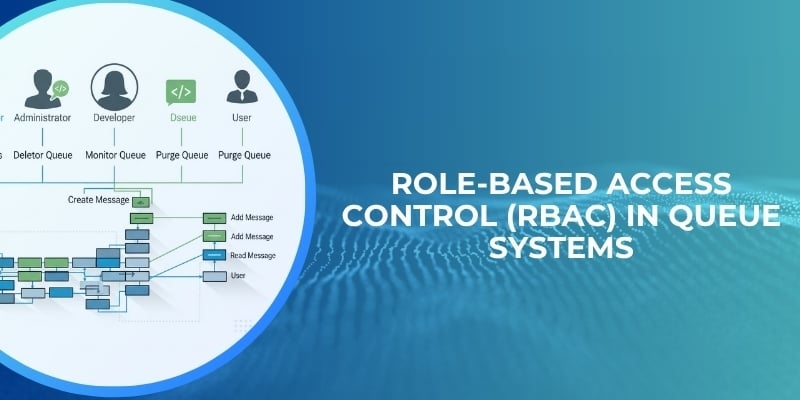
Role-Based Access Control (RBAC) is a security model that restricts system access based on a user’s role within the organization.
Instead of granting permissions to individual users one by one, permissions are assigned to roles. Users are then assigned to roles. This approach ensures that users have exactly the access they need to perform their jobs and nothing more.
In a queue management system, common roles include teller, branch manager, regional manager, system administrator, and auditor.
A teller role typically has permissions to view their own queue, call the next customer, complete service transactions, and add notes. A teller cannot see queue analytics for other branches, cannot change system configuration, and cannot delete customer records.
A branch manager role inherits teller permissions but adds the ability to view queue analytics for their branch, adjust service priorities, add or remove staff from the queue roster, and generate reports. A branch manager cannot change settings at other branches.
A regional manager role can view aggregated data across multiple branches but cannot access individual customer details or modify daily operations. A system administrator role has full access to all configuration settings, user accounts, and security logs. This role is limited to IT staff with background checks and additional MFA requirements.
RBAC reduces security incidents by limiting what each user can do. If a teller’s account is compromised, the attacker can only perform teller actions. They cannot view manager dashboards, change system settings, or access other branches. This containment limits damage.
A multi‑factor‑auth and RBAC best‑practice analysis notes that Role‑Based Access Control (RBAC) can reduce security incidents by up to 75% by limiting access to only what users need. The principle of least privilege, where users have minimum necessary permissions, is the core of RBAC. When roles are properly defined, the attack surface shrinks dramatically.
In multi-branch environments, RBAC becomes even more important. A queue system may have hundreds or thousands of users across dozens of locations. Without RBAC, administrators would have to manage permissions individually, a task that is error-prone and insecure.
With RBAC, creating a new user is simple: assign the appropriate role, and permissions are granted automatically. When a user changes roles, their permissions update automatically.
RBAC also supports audit compliance. Regulators want to see that access is restricted by job function. RBAC provides clear documentation of who has access to what, based on organizational structure. Audit logs show which users performed which actions, and RBAC ensures those users had legitimate reasons.
Data Protection in Queue Management Systems
Data protection refers to the practices and technologies that keep customer information safe from unauthorized access, alteration, or loss. In queue management systems, data protection covers the entire data lifecycle: collection, storage, transmission, processing, and deletion.
The importance of protecting customer data cannot be overstated. Queue systems store personally identifiable information (PII) such as names, phone numbers, email addresses, and sometimes national ID numbers.
In healthcare settings, they store protected health information (PHI) subject to HIPAA. In banking, they store financial data subject to GLBA and other regulations. In Europe, any customer data from EU residents is subject to GDPR.
Compliance and privacy regulations impose specific requirements for data protection. Organizations must implement technical and organizational measures to ensure data security.
They must notify authorities and affected individuals of breaches. They may face fines of up to 4% of global annual revenue for GDPR violations or millions of dollars for HIPAA violations.
Queue management systems must also protect data from internal threats. Not all breaches come from external attackers. An employee might accidentally view records they should not see, or maliciously export customer data before leaving the company. Data protection controls limit these risks.
Key Data Protection Practices

Following are the key data protection practices that secure queue management systems.
Encryption at Rest and in Transit
Encryption transforms readable data into unreadable ciphertext that can only be decrypted with a key. Data at rest refers to information stored on disks, databases, and backups. Data in transit refers to information moving across networks between systems.
Encryption at rest protects against physical theft of servers or hard drives. Even if an attacker steals the hardware, they cannot read the data without the decryption key.
Database encryption, file-level encryption, and full-disk encryption are common implementations. Encryption keys must be stored separately from the data, ideally in a hardware security module (HSM) or key management service.
Encryption in transit protects against network eavesdropping. When a user logs into a queue system from a branch or remote location, their session should be encrypted using TLS (Transport Layer Security). All API calls between the queue system and integrated CRM or banking platforms should also use TLS.
Without encryption, an attacker on the same network could capture passwords, customer data, and service records.
Cloud‑queue‑security guides (e.g., AWS, general‑cloud advice) state that encryption at rest and in transit is now a standard requirement for secure message queues, typically covering over 80% of recommended controls.
For queue management systems, encryption is an expectation, not an optional feature.
Secure Data Storage
In addition to encryption, secure data storage involves where and how data is kept. Data should be stored in geographically redundant, physically secure data centers with access controls, surveillance, and environmental protections. Cloud providers such as AWS, Azure, and Google Cloud offer certified data centers with SOC 2, ISO 27001, and other compliance attestations.
Data should be retained only as long as necessary. Queue systems should have automated data retention policies that delete records after a defined period, such as 90 days for check-in logs or 7 years for certain transaction records as required by law. Deleting data reduces the amount of sensitive information at risk.
Data minimization is another principle. Queue systems should collect only the data required for service. If a customer’s full address is not needed for queue management, that field should not be stored. Minimizing data reduces breach impact.
Data Access Monitoring
Monitoring who accesses data and when is essential for detecting and investigating security incidents.
Queue management systems should maintain comprehensive audit logs of all data access. Each log entry should include the user ID, timestamp, action performed (view, edit, delete), and the specific record accessed.
Monitoring systems can generate alerts for suspicious patterns. For example, if a user who normally accesses 50 records per day suddenly accesses 5000, the system should flag this as potential data exfiltration. If a user attempts to access records outside their branch or department, the system should log an exception.
Audit logs should be immutable, meaning they cannot be altered or deleted by users, including administrators. This ensures the integrity of evidence for investigations and compliance audits. Logs should be retained for extended periods, often 1–7 years, depending on regulations.
Backup and Recovery Systems
Data can be lost due to hardware failure, software bugs, natural disasters, or ransomware attacks. Regular backups are essential for restoring service and data after an incident. Queue management systems should implement automated, encrypted backups on a schedule appropriate to data criticality.
Backups should be stored in separate locations from the primary data, preferably in different geographic regions. This protects against site-wide disasters. Backup restoration should be tested regularly to ensure that data can be recovered within defined recovery time objectives (RTOs) and recovery point objectives (RPOs).
For queue systems, losing configuration data such as service rules, user roles, and branch settings would disrupt operations for hours or days. Backups enable rapid restoration.
Compliance and Regulatory Standards
Queue management systems should adhere to recognized security and compliance frameworks.
- SOC 2 (Service Organization Control 2) is the gold standard for SaaS systems, attesting that the vendor has appropriate controls for security, availability, processing integrity, confidentiality, and privacy.
- GDPR compliance is required for systems handling EU citizen data.
- HIPAA compliance is required for US healthcare data.
- PCI DSS applies if payment card information is processed.
Achieving and maintaining these certifications demonstrates commitment to security. Enterprise customers often require SOC 2 Type II reports as a condition of contract. Wavetec maintains SOC 2 compliance for its queue management and customer experience platforms.
How MFA, RBAC, and Data Protection Work Together
MFA, RBAC, and data protection are not independent controls. They form a layered security architecture that protects queue management systems from multiple threat vectors.
- MFA addresses the authentication layer. It ensures that only legitimate users can access the system, even if passwords are compromised. Without MFA, an attacker with a stolen password gets full access. With MFA, they are blocked.
- RBAC addresses the authorization layer. Once a user is authenticated, RBAC determines what they can do. It applies the principle of least privilege. Even if an attacker compromises a teller’s account, RBAC limits them to teller permissions. They cannot access administrative functions or other branches’ data.
- Data protection addresses the storage and transmission layers. Encryption ensures that if attackers bypass authentication (e.g., by exploiting a vulnerability) or steal physical media, they cannot read the data. Access monitoring detects unusual patterns that could indicate a breach. Backups ensure recovery after ransomware or data corruption.
Together, these layers create defense in depth. A single control failure does not lead to disaster.
- MFA stops credential theft.
- RBAC contains damage from compromised accounts.
- Encryption protects stolen data. Monitoring detects incidents quickly.
- Backups restore operations after attacks.
For queue management systems deployed in multi-branch, multi-user environments, this layered approach is essential. No single control is sufficient. Organizations must implement all three pillars to achieve enterprise-grade security.
Security Features in Wavetec Queue Management Solutions
Wavetec builds security into every layer of its queue management and customer journey platforms. The solutions are designed for enterprise customers with strict security and compliance requirements.
- Multi-Factor Authentication: Wavetec queue management supports MFA for all user accounts. Administrators can enforce MFA for specific roles or all users. Integration with SSO providers such as Okta, Azure AD, and Google Workspace allows centralized MFA policy management.
- Role-Based Access Control: Wavetec implements granular RBAC with predefined roles for tellers, branch managers, regional managers, administrators, and auditors. Custom roles can be created for specific organizational needs. Access can be restricted by branch, department, or service type. Permissions control specific actions: view queues, call customers, edit wait times, generate reports, change configurations, and delete records.
- Data Encryption: All customer data stored in Wavetec systems is encrypted at rest using AES-256. Data in transit is encrypted with TLS 1.3. Encryption keys are managed in secure key management services with strict access controls.
- Secure Data Storage: Wavetec cloud deployments use major cloud providers with SOC 2, ISO 27001, and PCI DSS certified data centers. Data is stored in geographically redundant configurations. Automated retention policies delete data after defined periods.
- Access Monitoring and Audit Logs: Wavetec systems maintain comprehensive audit trails of all user actions. Logs include user ID, timestamp, action, and affected record. Anomaly detection alerts are configurable. Logs are immutable and retained for compliance periods.
- Compliance Certifications: Wavetec maintains SOC 2 Type II certification for its queue management and customer journey platforms. The company adheres to GDPR privacy principles and supports HIPAA compliance for healthcare customers.
- Integration Security: APIs use OAuth 2.0 authentication and TLS encryption. Rate limiting prevents abuse. Wavetec works with customers to secure integrations with CRM, HIMS, and core banking systems.
Centralized security controls allow administrators to manage MFA policies, RBAC roles, and monitoring from a single dashboard. Reporting capabilities support internal audits and regulatory inspections.
For more on Wavetec’s secure customer journey solutions, see our article on customer journey management.
Case Study – Enhancing Security in a Multi-Branch Organization
BCI Bank, one of Chile’s largest financial institutions, operates an extensive network of branches serving thousands of customers daily.
With multiple users accessing the queue management system across locations, the bank required a secure, centralized platform to manage customer flow while protecting sensitive financial data.
In a multi-branch environment, ensuring that the right users have the right level of access (while maintaining visibility and control at a central level) is critical.
The bank needed a solution that could support secure access, protect customer information, and enforce consistent policies across all branches.
Challenges
- Managing system access across hundreds of branches introduced several security risks.
- Without structured controls, there was potential for unauthorized access to customer data, especially when multiple staff members with different roles used the same system. Ensuring that tellers, branch managers, and regional teams only accessed relevant data was a key concern.
- The bank also required stronger authentication mechanisms to prevent unauthorized logins, particularly in a system accessed across multiple locations. Password-only access created vulnerability to credential misuse.
- Additionally, maintaining data protection across branches was complex. Customer information needed to be securely stored, transmitted, and accessed without exposing it to unnecessary risk. The lack of centralized monitoring made it difficult to track system usage and detect anomalies in real time.
Solution
BCI Bank implemented Wavetec’s queue management system with built-in enterprise security controls, focusing on multi-factor authentication (MFA), role-based access control (RBAC), and data protection.
MFA was introduced to strengthen user authentication, ensuring that access to the system required more than just passwords. This added an extra layer of protection against unauthorized logins across all branches.
RBAC was configured to align with the bank’s organizational structure. Tellers were restricted to handling customer queues and service interactions at their assigned branches. Branch managers were granted access to branch-level analytics and operational controls, while regional teams could view aggregated performance data without accessing sensitive customer-level details. This ensured that each user operated strictly within their role.
Data protection measures were applied across the system, including encryption of data in transit and at rest. Customer information was secured throughout its lifecycle, from check-in to service completion.
Centralized dashboards provided real-time monitoring of system activity, enabling administrators to track access, identify unusual patterns, and maintain compliance with internal security policies.
Results
The implementation significantly strengthened security across the bank’s multi-branch operations.
Unauthorized access risks were reduced through layered authentication and strict role-based permissions. Even if credentials were compromised, access remained limited to the user’s assigned role, minimizing potential impact.
Data visibility was improved without compromising security. Staff had access to the information they needed, while sensitive data remained protected and restricted.
Operational control became more consistent across branches, with centralized policies ensuring uniform security standards. Monitoring capabilities allowed the bank to maintain oversight and respond proactively to potential risks.
As a result, BCI Bank achieved a secure, scalable queue management environment that supported both efficient customer service and enterprise-grade data protection; demonstrating how MFA, RBAC, and encryption can work together to protect modern, multi-branch operations.
Common Security Challenges in Queue Management Systems
Even with strong security features, organizations face challenges in implementing and maintaining secure queue systems.
- Managing user access across locations is difficult for organizations with many branches or clinics. Users transfer between locations, change roles, or leave the organization. Access must be updated promptly. Without automated provisioning, orphaned accounts accumulate, creating security holes. Integration with HR systems and identity management platforms helps.
- Ensuring compliance with multiple regulations (GDPR, HIPAA, PCI DSS, local laws) requires ongoing effort. Security controls must be documented, tested, and audited. Staff must be trained. Breach notification procedures must be in place. Small organizations may lack dedicated compliance resources.
- Protecting data in cloud environments shifts responsibility to the vendor. Organizations must trust that the cloud provider’s security is adequate. They must also understand the shared responsibility model: the vendor secures the infrastructure, but the customer secures their own access policies and data usage. Misconfigurations are a common cloud vulnerability.
- Balancing security and usability is a persistent tension. Strong MFA adds friction. Complex RBAC rules can confuse users. Strict data protection may slow performance. Security teams must find the right balance for their risk tolerance and user needs. User training and clear policies help.
Future of Security in Queue Management Systems
The security landscape is evolving. Several trends will shape the next generation of queue management system security.
- Zero-trust security models will replace traditional perimeter-based approaches. In zero trust, no user or device is trusted by default, regardless of location. Every access request is authenticated, authorized, and encrypted. This model is ideal for queue systems accessed from branches, home offices, and mobile devices.
- AI-driven threat detection will analyze user behavior patterns to identify anomalies. Machine learning models will learn what normal access looks like for each role and flag deviations. AI will also detect sophisticated attacks that evade signature-based controls.
- Advanced identity management will move beyond passwords and even MFA. Passwordless authentication using biometrics or hardware tokens will become common. Continuous authentication will monitor user behavior throughout a session, not just at login.
- Continuous monitoring systems will provide real-time visibility into security posture. Organizations will receive alerts about misconfigurations, vulnerable software versions, and potential breaches as they happen, not hours or days later. Automated remediation will respond to some threats without human intervention.
FAQs
What is MFA in queue management systems?
MFA (multi-factor authentication) requires users to provide two or more verification factors, such as a password plus a one-time code from a smartphone, to access the queue system. It prevents unauthorized access even if passwords are stolen.
How does RBAC improve security?
RBAC (role-based access control) limits what each user can do based on their job role. A teller cannot access manager functions, and a branch manager cannot access other branches’ data. This containment reduces damage from compromised accounts and prevents internal misuse.
Why is data encryption important in queue systems?
Encryption protects customer data from unauthorized access. Data at rest (stored on disks) and data in transit (moving across networks) are encrypted so that even if attackers gain access, they cannot read the information without the decryption key.
What security standards should queue systems follow?
Queue systems should follow SOC 2 (for SaaS security), GDPR (for EU data privacy), HIPAA (for US healthcare data), and industry-specific regulations. Encryption, MFA, RBAC, audit logs, and backup/recovery are standard expectations.
How can businesses secure customer data in queue systems?
Businesses should implement MFA for all users, enforce RBAC with least privilege, encrypt data at rest and in transit, maintain audit logs, perform regular backups, and comply with relevant regulations. Choosing a vendor with SOC 2 certification and robust security features is essential.
Conclusion
Queue management system security is a basic requirement for any organization that handles customer data.
- Multi-factor authentication stops credential theft.
- Role-based access control limits damage from compromised accounts.
- Data protection keeps information safe from unauthorized access and loss.
These three pillars work together to create defense in depth, protecting against external attackers, insider threats, and operational failures.
Wavetec builds these security features into its queue management, customer journey, and appointment booking solutions, offering enterprise-grade protection for banks, healthcare providers, government agencies, and retail chains.
Organizations that prioritize security earn customer trust, pass regulatory audits, and avoid the devastating costs of data breaches.
As threats evolve, so must security, but the foundation remains the same: MFA, RBAC, and data protection are the non-negotiable essentials for any modern queue management system.
BOOK A FREE DEMO