The rapid adoption of digital and remote healthcare has transformed how patients access medical services. Telemedicine platforms, electronic health records, mobile health applications, and self-service kiosks have made care more convenient and accessible than ever before.
However, this digital transformation has also created new vulnerabilities. Patient data now flows across numerous systems, devices, and networks, exponentially increasing the points where breaches can occur.
Cybercriminals view healthcare data as extremely valuable, containing personal identifiers, financial information, and sensitive medical histories that can be sold or used for fraud.
For healthcare providers, protecting patient information is essential for maintaining patient trust, ensuring continuity of care, and avoiding the devastating operational and financial consequences of a data breach.
This article provides a practical guide to understanding and strengthening data security in healthcare, helping organizations manage the complex landscape of digital healthcare security while protecting the patient data protection that is fundamental to the healing relationship.
In 2024, over 300 million patient records were compromised in U.S. healthcare breaches, marking a 26% increase from 2023 and the highest ever recorded.
What Is Data Security in Healthcare?

Data security in healthcare refers to the policies, practices, and technologies designed to protect patient information from unauthorized access, use, disclosure, disruption, modification, or destruction.
It includes the entire lifecycle of patient data, from the moment it is created during a clinical encounter to its storage, transmission, and eventual archival or deletion.
Healthcare data security involves protecting data across all forms and locations: electronic health records in core clinical systems, data transmitted during telemedicine consultations, information stored on mobile devices, and even physical records in filing cabinets.
The goal is to ensure the confidentiality, integrity, and availability of patient information.
- Confidentiality means that only authorized individuals can access the data.
- Integrity ensures that the data is accurate and has not been tampered with.
- Availability guarantees that authorized users can access the data when needed for patient care.
Why Data Security Matters in Digital and Remote Healthcare
The shift toward digital healthcare security and remote care models has changed the security arena. Telemedicine platforms, cloud-based electronic health records, remote patient monitoring devices, and patient portals all create new entry points for attackers.
Each connected device, each remote access point, and each third-party integration expands what security professionals call the attack surface.
Remote healthcare security is particularly challenging because care now extends beyond the traditional boundaries of hospitals and clinics. Clinicians work from home, patients connect from their living rooms, and data travels across networks that healthcare organizations do not control.
Healthcare data is uniquely valuable on the black market. Unlike credit card numbers, which can be canceled and reissued quickly, medical records contain permanent information such as social security numbers, birth dates, and biometric data. This information can be used for identity theft, insurance fraud, and prescription drug diversion for years after a breach.
The consequences of inadequate security extend far beyond financial losses. Breaches disrupt patient care, erode trust in healthcare institutions, and can even lead to direct patient harm if medical records are altered or if critical systems are rendered unavailable during a ransomware attack.
Key Threats to Patient Information in Healthcare
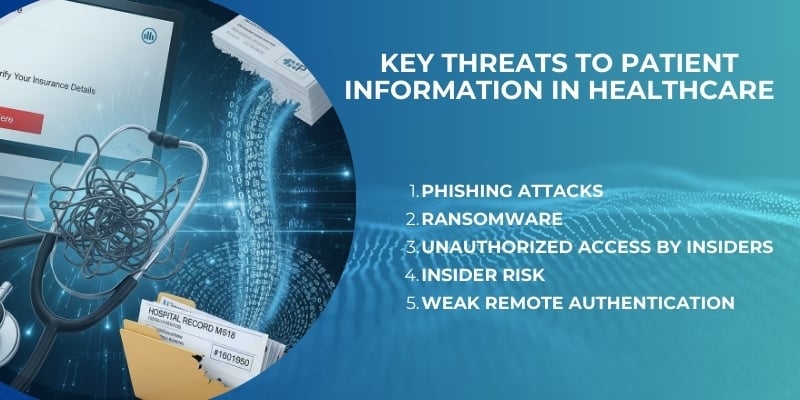
Understanding the threat landscape is essential for building effective defenses. Healthcare cybersecurity professionals must guard against a range of threats, each requiring different mitigation strategies.
- Phishing attacks remain the most common entry point for healthcare breaches. Attackers send deceptive emails that appear to come from trusted sources such as hospital leadership, IT departments, or familiar vendors. These emails trick employees into revealing login credentials or clicking malicious links that install malware.
- Ransomware has become increasingly prevalent in healthcare. Attackers encrypt critical systems and demand payment for their release. When hospitals lose access to electronic health records, scheduling systems, or communication tools, patient care is immediately impacted and some organizations have been forced to divert ambulances.
- Unauthorized access by insiders, whether malicious or accidental, poses a significant risk. Employees with legitimate access may view records outside the scope of their duties out of curiosity, or they may inadvertently expose data through poor security practices such as sharing passwords.
- Insider risk extends beyond employees to contractors, vendors, and business partners who have access to healthcare systems. These third parties may have weaker security practices than the healthcare organization itself, creating vulnerabilities that attackers can exploit.
- Weak remote authentication has become a critical vulnerability as more healthcare workers access systems from home. Without strong multi-factor authentication, stolen credentials can give attackers direct access to patient data.
Phishing Attacks and Human Risk in Healthcare
Phishing attacks in healthcare exploit the human element, which remains the most difficult vulnerability to eliminate. In 2024, 8% of healthcare workers opened phishing emails, contributing to over 90% of cyberattacks on the sector being phishing-related.
This statistic reveals a fundamental truth about healthcare cybersecurity: technology alone cannot protect patient data. The people who interact with that data every day are both the first line of defense and the most likely point of failure.
Phishing emails have become increasingly sophisticated. They often appear to come from trusted sources and may contain personalized information, making them highly convincing.
When an employee clicks a malicious link, attackers gain a foothold inside the organization’s network. From there, they can escalate privileges and eventually access patient data.
Addressing this threat requires a combination of technical controls and ongoing education. Technical measures such as advanced email filtering and endpoint detection can block many phishing attempts. However, human awareness remains essential.
Regular security training that teaches employees how to recognize phishing attempts and report them appropriately reduces the likelihood of successful attacks.
Securing Patient Data Across Digital Care Channels
Modern healthcare delivers care through an increasingly diverse set of channels. Patients interact with providers through telemedicine platforms, patient portals, mobile apps, and text messaging.
Within healthcare facilities, they engage with self-service kiosks for check-in and call centers for scheduling. Each of these channels generates, transmits, or accesses patient information.
A secure healthcare system treats every channel as part of an integrated whole. When a patient checks in at a self-service kiosk, the system must authenticate their identity, retrieve relevant information from the electronic health record, and update their visit status. All of this data exchange must be encrypted and logged.
Achieving consistency requires a unified security architecture. Single sign-on solutions allow users to authenticate once and access multiple systems securely. Centralized identity and access management ensures that permissions are consistently enforced.
This approach to customer journey management ensures that patient data remains protected at every touchpoint.
Data Security in Telemedicine and Remote Care
The explosive growth of telemedicine has created new security challenges. Telehealth data security requires specialized controls tailored to virtual care delivery. Unlike in-person visits, telemedicine consultations happen in locations over which providers have no physical control.
- Secure video platforms are the foundation of telemedicine security. These platforms must provide end-to-end encryption, ensuring that no third party can intercept or view the consultation. They should also offer features such as waiting rooms and meeting locks.
- Encrypted communication extends beyond video to all data transmitted during telemedicine encounters. Encryption must protect data both in transit and at rest.
- Authenticated access is critical. Patients must verify their identity before joining a consultation, and providers must be confident they are connecting with the correct patient. Multi-factor authentication for provider access adds an additional layer of security.
- Device security is another important consideration. Healthcare organizations should provide guidance to patients on securing their devices and ensure that provider devices meet minimum security standards.
Protecting Electronic Health Records
Electronic health records are the crown jewels of healthcare data. They contain comprehensive patient histories, including diagnoses, treatments, medications, and test results. EHR security is therefore a top priority.
- Access control is the first line of defense. Role-based access control ensures that users can only view and modify information necessary for their job functions. A receptionist may need access to demographic information but not clinical notes.
- Encryption protects EHR data both at rest and in transit. Even if an attacker gains access to storage systems, encrypted data remains unreadable without the appropriate cryptographic keys.
- Audit logs provide a record of who accessed what information, when, and from where. Comprehensive logging deters inappropriate access and enables investigation when suspicious activity occurs.
- Role-based permissions ensure that users have only the minimum access necessary, a principle known as least privilege. When employees change roles or leave, their access must be promptly updated or revoked.
Compliance, Privacy, and Regulatory Responsibilities
Healthcare organizations operate within a complex regulatory environment designed to protect patient privacy. The principles of HIPAA compliance provide a useful framework for understanding healthcare privacy obligations.
- Healthcare privacy requires that patients have control over their information. They must be notified about how their data will be used and must provide consent for uses beyond treatment and payment. Patients also have the right to access their own records and request corrections.
- Auditability means that organizations must demonstrate compliance to regulators. This requires comprehensive documentation of security policies, procedures, and controls. Regular risk assessments help identify vulnerabilities and document the steps taken to address them.
- Accountability extends throughout the organization. Leadership must establish a culture of security, provide adequate resources for compliance, and ensure that security is integrated into all aspects of operations.
Best Practices for Improving Data Security in Healthcare
Improving healthcare IT security requires a comprehensive approach addressing technology, processes, and people. These data protection best practices provide a framework for strengthening security posture.
- Multi-factor authentication should be required for all users accessing healthcare systems. Requiring something the user knows plus something they have dramatically reduces the risk of credential theft.
- Least-privilege access ensures users have only necessary permissions. Regular access reviews help identify and remove excessive permissions that accumulate over time.
- Encryption must be applied consistently to all sensitive data. Strong encryption standards make stolen data unusable to attackers.
- Staff training is essential because human error remains a leading cause of breaches. Training should be engaging, relevant, and frequent, covering phishing recognition and proper data handling.
- Continuous monitoring provides real-time visibility into security events. Security information and event management systems apply analytics to detect anomalies and potential threats.
Balancing Strong Security with Patient Experience
A common concern is that strong security will create friction degrading the patient experience. However, security and experience are not mutually exclusive. Secure digital healthcare can be designed to be both protective and seamless.
Multi-factor authentication can be streamlined using biometrics such as fingerprint or facial recognition, which are both highly secure and convenient. Single sign-on allows patients to authenticate once and access multiple services without repeated logins.
Background security processes such as encryption operate invisibly without affecting user experience. When security measures are explained as protections for sensitive information, patients accept them willingly.
Common Challenges in Healthcare Data Security
Healthcare organizations face persistent healthcare security challenges that complicate protection efforts.
- Legacy systems are pervasive in healthcare. Many critical systems were designed before modern security threats existed and cannot easily be updated. Organizations must implement compensating controls such as network segmentation.
- Workforce awareness gaps persist despite training. Healthcare workers focused on patient care may take shortcuts that create vulnerabilities. Building a security culture requires consistent messaging and leadership examples.
- Vendor sprawl creates security complexity. Each vendor represents potential risk, particularly those with access to patient data. Managing vendor security assessments is a significant challenge.
- Managing secure remote access has become more difficult as remote work expands. Each remote user creates a potential entry point requiring investment in VPNs and endpoint security tools.
Future of Data Security in Digital Healthcare
The future of data security in healthcare will be shaped by emerging technologies and evolving threat landscapes.
- Zero-trust security is replacing the traditional perimeter-based model. In a zero-trust architecture, no user or device is trusted by default. Every access request is authenticated and authorized based on identity and context.
- Identity-first access puts identity at the center of security. Strong identity management enables granular access control across diverse systems and locations.
- AI-assisted threat detection will become increasingly important. Machine learning algorithms can analyze vast amounts of security data to identify patterns and anomalies that human analysts might miss.
- Secure-by-design healthcare platforms will become the expectation. New technologies will incorporate security from the earliest stages of design rather than adding it as an afterthought.
FAQs
What is data security in healthcare?
Data security in healthcare refers to the policies, technologies, and practices that protect patient information from unauthorized access, use, and disclosure across all systems and channels. It ensures sensitive medical data remains confidential, accurate, and available to authorized users when needed.
Why is patient data at high risk in digital healthcare?
Patient data is valuable to cybercriminals for identity theft and fraud. The expansion of digital channels, remote access, and connected devices has increased the attack surface, creating more opportunities for breaches while making systems more complex to secure.
How does telemedicine impact data security?
Telemedicine introduces new security considerations including secure video platforms, encrypted communications, authenticated access, and device security. Each virtual consultation creates potential vulnerabilities that must be addressed through specialized controls.
What role do healthcare staff play in cybersecurity?
Healthcare staff are both the first line of defense and the most common point of failure. Their actions determine whether security policies are followed. Regular training and clear procedures help staff recognize threats and protect patient data.
How can providers reduce data breach risks?
Providers can reduce risks through multi-factor authentication, least-privilege access controls, encryption of sensitive data, comprehensive staff training, continuous security monitoring, and regular risk assessments addressing technology, processes, and people.
Conclusion
Data security in healthcare is fundamental to patient trust, regulatory compliance, and uninterrupted digital care. As healthcare becomes increasingly digital and remote, risks to patient information multiply.
Breaches disrupt operations, damage reputations, and can directly harm patients. Yet with thoughtful implementation of security controls, consistent staff training, and a culture that prioritizes protection, healthcare organizations can significantly reduce these risks.
Investing in digital healthcare security is investing in the future of healthcare itself.
Every provider, every system, and every interaction must be secured with the understanding that protecting patient data is inseparable from protecting patients.
BOOK A FREE DEMO





